Debian 12 Server Setup: Essential Post-Installation Steps
Mar 13, 2025 am 11:55 AM
Welcome to our detailed guide on what to do after installing Debian 12 server. If you've just set up a new Debian server, you're probably wondering what steps to take next. This guide will teach you essential post installation steps for a minimal Debian 12 server installation, ensuring your server is secure, up-to-date, and ready for use.
From configuring software repositories to hardening SSH and setting up firewalls, we'll cover everything you need to get your Debian 12 server running smoothly.
Table of Contents
1. Configure Software Repositories
If this is a new minimal Debian installation, you should configure the software repositories.
Edit the /etc/apt/sources.list file:
nano /etc/apt/sources.list
Replace the contents with the following (or ensure they are present):
deb http://deb.debian.org/debian bookworm main contrib non-free non-free-firmware deb-src http://deb.debian.org/debian bookworm main contrib non-free non-free-firmware deb http://deb.debian.org/debian bookworm-updates main contrib non-free non-free-firmware deb-src http://deb.debian.org/debian bookworm-updates main contrib non-free non-free-firmware deb http://security.debian.org/debian-security bookworm-security main contrib non-free non-free-firmware deb-src http://security.debian.org/debian-security bookworm-security main contrib non-free non-free-firmware
Save and close the file.
Update the package list to ensure you have the latest information about available packages.
apt update
2. Upgrade Existing Packages
Upgrade the existing packages to their latest versions.
apt upgrade -y apt full-upgrade -y
3. Install sudo
sudo is not installed in the minimal Debian installation. Since you don't have sudo access, you'll need to install it as the root user.
apt install sudo -y
4. Create a New User and Add to sudo Group
Create a new user and add them to the sudo group.
adduser ostechnix usermod -aG sudo ostechnix
Replace ostechnix with your actual username.
Once a new user is created, switch to the new user account.
su - ostechnix
Again, replace the username with your own.
Test that the new user has sudo access by running a command with sudo.
sudo -v
For more details, check the following guide:
- How To Add, Delete, And Grant Sudo Privileges To Users In Debian 12
5. Set Up SSH Keys (Optional)
If you want to use SSH keys for authentication, follow these steps.
On your local machine, generate an SSH key pair:
ssh-keygen
Copy the public key to your Debian server:
ssh-copy-id newusername@server_ip
Replace the username and IP address with actual values in the above command.
6. Secure SSH
Edit the SSH configuration to enhance security.
sudo nano /etc/ssh/sshd_config
Make the following changes:
- Set PermitRootLogin to no
- Set PasswordAuthentication to no (if you plan to use SSH keys)
- Set AllowUsers to specify allowed users
- Set Port to a non-default port (optional but recommended)
PermitRootLogin no PasswordAuthentication no AllowUsers newusername Port 2222 # Example non-default port
Replace the username and port number with your own. Save and close the file.
Restart the SSH service:
sudo systemctl restart ssh
7. Install Essential Packages
Install some essential packages for system management and monitoring. I intend to keep a minimal Debian setup for myself, so I installed the following:
sudo apt install -y vim htop net-tools curl wget git
8. Configure Time Synchronization
Set up time synchronization using systemd-timesyncd or ntp.
8.1. Using systemd-timesyncd:
sudo apt install systemd-timesyncd sudo timedatectl set-ntp true
Verify if the time synchronization is setup correctly by running timedatectl command:
$ timedatectl Local time: Tue 2024-08-27 18:54:21 IST Universal time: Tue 2024-08-27 13:24:21 UTC RTC time: Tue 2024-08-27 13:24:21 Time zone: Asia/Kolkata (IST, 0530)<strong>System clock synchronized: yes</strong> <strong> NTP service: active</strong> RTC in local TZ: no
8.2. Using ntp:
You can also configure time synchronization using ntp. To do so, run the following commands:
sudo apt install ntp -y sudo systemctl enable ntp sudo systemctl start ntp
9. Set Up a Firewall
This step is highly recommended if you connect your server to Internet. You should configure a firewall to restrict incoming and outgoing traffic.
9.1. Using ufw (Uncomplicated Firewall):
UFW is a command line front-end to manage iptables. It provides a framework for managing and manipulating netfilter firewall.
Run the following commands one by one to quickly setup ufw firewall, deny all incoming connections and allow only ssh connection.
sudo apt install ufw -y sudo ufw default deny incoming sudo ufw default allow outgoing sudo ufw allow ssh sudo ufw enable
For detailed usage about ufw, I recommend you to refer the following guide:
- How To Setup Firewall With UFW On Linux
10. Enable Automatic Security Updates
Enable automatic security updates to keep your system secure.
sudo apt install -y unattended-upgrades sudo dpkg-reconfigure -plow unattended-upgrades
For more details, check the following guide:
- Enable Automatic Security Updates In Debian 12
11. Set Up Fail2Ban (Optional)
Install and configure monitoring like Fail2ban to prevent your servers from SSH Brute-force attacks.
sudo apt install -y fail2ban sudo systemctl enable fail2ban sudo systemctl start fail2ban
This is just enough for basic monitoring. For more detailed configuration, check our Fail2ban guide:
- A Comprehensive Guide to Install and Configure Fail2ban in Linux for Improved Security.
NOTE:It is usually not necessary to use Fail2Ban with sshd if only public key authentication is enabled. If you have already configured SSH key-based authentication, fail2ban is not required.
12. Additional Configuration
You should have set these during the installation. If you want to set up different values, you can do so.
- Network Configuration:Review and configure network settings if necessary.
- Hostname:Set a meaningful hostname.
- DNS:Configure DNS settings in/etc/resolv.conf.
13. Reboot the System
Finally, reboot your system to apply all changes.
sudo reboot
By following these steps, you will have configured your software repositories, installed sudo, created a new user with sudo access, and set up your system with essential security and management tools.
Did I miss any steps in Debian 12 server post installation? Please share your inputs via the comment section below. I will test them and update the guide accordingly.
Related Read:
- DebPostInstall: Debian And Ubuntu Server Post Install Script
The above is the detailed content of Debian 12 Server Setup: Essential Post-Installation Steps. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 SCP Linux Command – Securely Transfer Files in Linux
Jun 20, 2025 am 09:16 AM
SCP Linux Command – Securely Transfer Files in Linux
Jun 20, 2025 am 09:16 AM
Linux administrators should be familiar with the command-line environment. Since GUI (Graphical User Interface) mode in Linux servers is not commonly installed.SSH may be the most popular protocol to enable Linux administrators to manage the servers
 Install LXC (Linux Containers) in RHEL, Rocky & AlmaLinux
Jul 05, 2025 am 09:25 AM
Install LXC (Linux Containers) in RHEL, Rocky & AlmaLinux
Jul 05, 2025 am 09:25 AM
LXD is described as the next-generation container and virtual machine manager that offers an immersive for Linux systems running inside containers or as virtual machines. It provides images for an inordinate number of Linux distributions with support
 How To Install R Programming Language in Linux
Jun 23, 2025 am 09:51 AM
How To Install R Programming Language in Linux
Jun 23, 2025 am 09:51 AM
R is a widely-used programming language and software environment designed for developing statistical and graphical computing tools within data science. It closely resembles the S programming language and environment, with R serving as an alternative
 7 Ways to Speed Up Firefox Browser in Linux Desktop
Jul 04, 2025 am 09:18 AM
7 Ways to Speed Up Firefox Browser in Linux Desktop
Jul 04, 2025 am 09:18 AM
Firefox browser is the default browser for most modern Linux distributions such as Ubuntu, Mint, and Fedora. Initially, its performance might be impressive, however, with the passage of time, you might notice that your browser is not as fast and resp
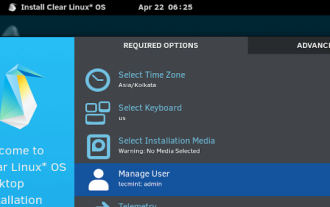 Clear Linux Distro - Optimized for Performance and Security
Jul 02, 2025 am 09:49 AM
Clear Linux Distro - Optimized for Performance and Security
Jul 02, 2025 am 09:49 AM
Clear Linux OS is the ideal operating system for people – ahem system admins – who want to have a minimal, secure, and reliable Linux distribution. It is optimized for the Intel architecture, which means that running Clear Linux OS on AMD sys
 How to create a self-signed SSL certificate using OpenSSL?
Jul 03, 2025 am 12:30 AM
How to create a self-signed SSL certificate using OpenSSL?
Jul 03, 2025 am 12:30 AM
The key steps for creating a self-signed SSL certificate are as follows: 1. Generate the private key, use the command opensslgenrsa-outselfsigned.key2048 to generate a 2048-bit RSA private key file, optional parameter -aes256 to achieve password protection; 2. Create a certificate request (CSR), run opensslreq-new-keyselfsigned.key-outselfsigned.csr and fill in the relevant information, especially the "CommonName" field; 3. Generate the certificate by self-signed, and use opensslx509-req-days365-inselfsigned.csr-signk
 How to Hide Files and Directories in Linux
Jun 26, 2025 am 09:13 AM
How to Hide Files and Directories in Linux
Jun 26, 2025 am 09:13 AM
Do you sometimes share your Linux desktop with family, friends, or coworkers? If so, you may want to hide some personal files and folders. The challenge is figuring out how to conceal these files on a Linux system.In this guide, we will walk through
 How to extract a .tar.gz or .zip file?
Jul 02, 2025 am 12:52 AM
How to extract a .tar.gz or .zip file?
Jul 02, 2025 am 12:52 AM
Decompress the .zip file on Windows, you can right-click to select "Extract All", while the .tar.gz file needs to use tools such as 7-Zip or WinRAR; on macOS and Linux, the .zip file can be double-clicked or unzip commanded, and the .tar.gz file can be decompressed by tar command or double-clicked directly. The specific steps are: 1. Windows processing.zip file: right-click → "Extract All"; 2. Windows processing.tar.gz file: Install third-party tools → right-click to decompress; 3. macOS/Linux processing.zip file: double-click or run unzipfilename.zip; 4. macOS/Linux processing.tar






