What is the principle of polymorphism in java
Jan 02, 2020 am 10:12 AM
What is polymorphism?
Polymorphism refers to which class instance object a reference variable will point to. The method call issued by the reference variable is a method implemented in which class. This must be determined during the running of the program. .
Because the specific class is determined when the program is running, the reference variable can be bound to various class implementations without modifying the source program code, resulting in the specific method called by the reference changing. This change means that the specific code bound to the program when it is running can be changed without modifying the program code, allowing the program to select multiple running states. This is polymorphism.
(Free online learning video tutorial sharing: java online learning)
Features:
points to the parent class of the subclass Since the reference is upwardly transformed, it can only access methods and properties owned by the parent class. For methods that exist in the subclass but not in the parent class, the reference cannot be used, even if the method is overloaded.
If the subclass overrides some methods in the parent class, when calling these methods, the methods defined in the subclass must be used (dynamic connection, dynamic calling).
There are three necessary conditions for Java to achieve polymorphism: inheritance, rewriting, and upward transformation.
The priority method called, the priority is: this.show(O), super.show(O), this.show((super)O), super.show((super )O).
The implementation principle of polymorphism
The invocation of object methods in Java is implemented by relying on the method table in the class information.
In general, when a method of an object is called, the JVM looks up the method table of the object class to determine the direct reference address of the method, and only then actually calls the method after having the address.
The super class inherits the method of the parent class. If the method is not Overriding, the call will point to the method of the parent class. If Overrding this method, it points to the code area of ??the class, but the super class will have the method table of the parent class.
We know that when a Java program is running, class-related information is placed in the method area. Among this information is an area called a method table. This table contains information about all methods defined by the type and points to these Pointer to the actual code of the method.
As shown in the figure:
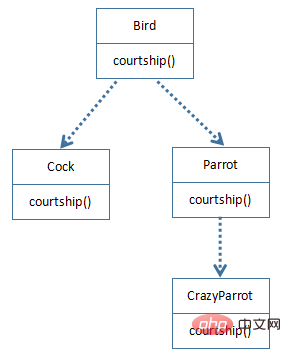
When the four classes Bird, Cock, Parrot and CrazyParrot are loaded into the method area of ??the Java virtual machine, The method area contains information about these four classes. The following figure shows an example of the method table of each class.
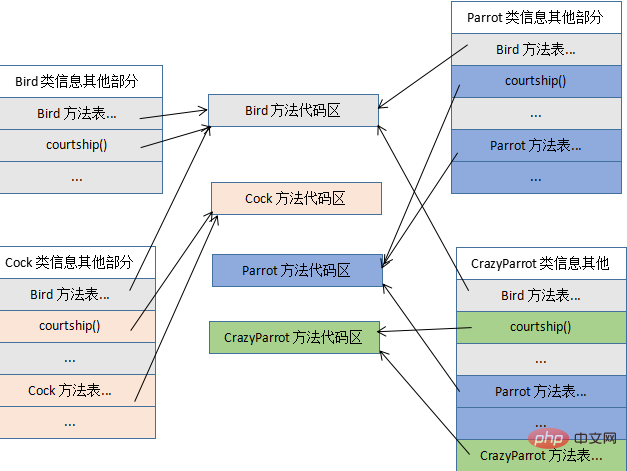
From the figure we can see that the class information method tables of Cock, Parrot and CrazyParrot contain methods inherited from Bird. CrazyParrot's method table contains methods inherited from Parrot. In addition, each class also has its own methods.
Pay attention to the specific method code area pointed to by the method table entry. For the polymorphic Overriding method courtship(), although the location of the courtship() entry in the method tables of Cock, Parrot and CrazyParrot belongs to the part inherited from the Bird method table, it points to a different method code area.
Related article tutorial sharing: Java language introduction
The above is the detailed content of What is the principle of polymorphism in java. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)
 How to handle transactions in Java with JDBC?
Aug 02, 2025 pm 12:29 PM
How to handle transactions in Java with JDBC?
Aug 02, 2025 pm 12:29 PM
To correctly handle JDBC transactions, you must first turn off the automatic commit mode, then perform multiple operations, and finally commit or rollback according to the results; 1. Call conn.setAutoCommit(false) to start the transaction; 2. Execute multiple SQL operations, such as INSERT and UPDATE; 3. Call conn.commit() if all operations are successful, and call conn.rollback() if an exception occurs to ensure data consistency; at the same time, try-with-resources should be used to manage resources, properly handle exceptions and close connections to avoid connection leakage; in addition, it is recommended to use connection pools and set save points to achieve partial rollback, and keep transactions as short as possible to improve performance.
 How to work with Calendar in Java?
Aug 02, 2025 am 02:38 AM
How to work with Calendar in Java?
Aug 02, 2025 am 02:38 AM
Use classes in the java.time package to replace the old Date and Calendar classes; 2. Get the current date and time through LocalDate, LocalDateTime and LocalTime; 3. Create a specific date and time using the of() method; 4. Use the plus/minus method to immutably increase and decrease the time; 5. Use ZonedDateTime and ZoneId to process the time zone; 6. Format and parse date strings through DateTimeFormatter; 7. Use Instant to be compatible with the old date types when necessary; date processing in modern Java should give priority to using java.timeAPI, which provides clear, immutable and linear
 Comparing Java Frameworks: Spring Boot vs Quarkus vs Micronaut
Aug 04, 2025 pm 12:48 PM
Comparing Java Frameworks: Spring Boot vs Quarkus vs Micronaut
Aug 04, 2025 pm 12:48 PM
Pre-formanceTartuptimeMoryusage, Quarkusandmicronautleadduetocompile-Timeprocessingandgraalvsupport, Withquarkusoftenperforminglightbetterine ServerLess scenarios.2.Thyvelopecosyste,
 go by example http middleware logging example
Aug 03, 2025 am 11:35 AM
go by example http middleware logging example
Aug 03, 2025 am 11:35 AM
HTTP log middleware in Go can record request methods, paths, client IP and time-consuming. 1. Use http.HandlerFunc to wrap the processor, 2. Record the start time and end time before and after calling next.ServeHTTP, 3. Get the real client IP through r.RemoteAddr and X-Forwarded-For headers, 4. Use log.Printf to output request logs, 5. Apply the middleware to ServeMux to implement global logging. The complete sample code has been verified to run and is suitable for starting a small and medium-sized project. The extension suggestions include capturing status codes, supporting JSON logs and request ID tracking.
 How does garbage collection work in Java?
Aug 02, 2025 pm 01:55 PM
How does garbage collection work in Java?
Aug 02, 2025 pm 01:55 PM
Java's garbage collection (GC) is a mechanism that automatically manages memory, which reduces the risk of memory leakage by reclaiming unreachable objects. 1.GC judges the accessibility of the object from the root object (such as stack variables, active threads, static fields, etc.), and unreachable objects are marked as garbage. 2. Based on the mark-clearing algorithm, mark all reachable objects and clear unmarked objects. 3. Adopt a generational collection strategy: the new generation (Eden, S0, S1) frequently executes MinorGC; the elderly performs less but takes longer to perform MajorGC; Metaspace stores class metadata. 4. JVM provides a variety of GC devices: SerialGC is suitable for small applications; ParallelGC improves throughput; CMS reduces
 Using HTML `input` Types for User Data
Aug 03, 2025 am 11:07 AM
Using HTML `input` Types for User Data
Aug 03, 2025 am 11:07 AM
Choosing the right HTMLinput type can improve data accuracy, enhance user experience, and improve usability. 1. Select the corresponding input types according to the data type, such as text, email, tel, number and date, which can automatically checksum and adapt to the keyboard; 2. Use HTML5 to add new types such as url, color, range and search, which can provide a more intuitive interaction method; 3. Use placeholder and required attributes to improve the efficiency and accuracy of form filling, but it should be noted that placeholder cannot replace label.
 Comparing Java Build Tools: Maven vs. Gradle
Aug 03, 2025 pm 01:36 PM
Comparing Java Build Tools: Maven vs. Gradle
Aug 03, 2025 pm 01:36 PM
Gradleisthebetterchoiceformostnewprojectsduetoitssuperiorflexibility,performance,andmoderntoolingsupport.1.Gradle’sGroovy/KotlinDSLismoreconciseandexpressivethanMaven’sverboseXML.2.GradleoutperformsMaveninbuildspeedwithincrementalcompilation,buildcac
 go by example defer statement explained
Aug 02, 2025 am 06:26 AM
go by example defer statement explained
Aug 02, 2025 am 06:26 AM
defer is used to perform specified operations before the function returns, such as cleaning resources; parameters are evaluated immediately when defer, and the functions are executed in the order of last-in-first-out (LIFO); 1. Multiple defers are executed in reverse order of declarations; 2. Commonly used for secure cleaning such as file closing; 3. The named return value can be modified; 4. It will be executed even if panic occurs, suitable for recovery; 5. Avoid abuse of defer in loops to prevent resource leakage; correct use can improve code security and readability.






