 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Permissions and access control strategies that you need to pay attention to before building a web server on CentOS
Permissions and access control strategies that you need to pay attention to before building a web server on CentOS
Permissions and access control strategies that you need to pay attention to before building a web server on CentOS
Aug 05, 2023 am 11:13 AMPermissions and access control policies that you need to pay attention to before building a web server on CentOS
In the process of building a web server, permissions and access control policies are a very important part. Correctly setting permissions and access control policies can protect the security of the server and prevent unauthorized users from accessing sensitive data or improperly operating the server. This article will introduce the permissions and access control strategies that need to be paid attention to when building a web server under the CentOS system, and provide corresponding code examples.
- User and Group Management
First, we need to create a user specifically used to run the web server and add it to the appropriate group. Create a user named "webuser" in the system by running the following command:
sudo useradd webuser
Next, we can add the webuser user to the www-data group (for Apache server) using the following command:
sudo usermod -a -G www-data webuser
- Settings of file and directory permissions
When building a web server, we need to ensure that the files and directories on the server have appropriate permissions. Normally, web server users only need permission to read files and execute directories, not write permissions.
The following is an example of setting directory permissions. Suppose we want to place the website files in the /var/www/html directory:
sudo chown -R webuser:www-data /var/www/html sudo chmod -R 755 /var/www/html
The above command sets the owner of the /var/www/html directory to the webuser user and the group to the www-data group. At the same time, the permissions of the directory are set to 755, that is, the owner has read, write, and execute permissions, while the group and other users only have read and execute permissions.
- Access control policy
In addition to file and directory permissions, we also need to set access control policies to control access to the web server. There are mainly the following ways to achieve this.
(1) Use configuration files to control access
In the Apache server, access permissions can be controlled through configuration files. For example, you can use the "Require" directive to restrict access to specific IP addresses. Here is an example of allowing only specific IP addresses to access a website:
<Directory /var/www/html>
Order deny,allow
Deny from all
Allow from 192.168.1.100
</Directory>The above configuration will deny all access requests except those with IP address 192.168.1.100.
(2) Use firewall to control access
Another way to control access is to use firewall rules. In CentOS systems, you can use the firewall-cmd command to set firewall rules. Here is an example to only allow HTTP access from a specific IP address:
sudo firewall-cmd --zone=public --add-rich-rule='
rule family="ipv4"
source address="192.168.1.100"
port protocol="tcp" port="80" accept'The above command will allow the host with IP address 192.168.1.100 to access the HTTP service.
Summary:
Before building a web server, we must pay attention to the settings of permissions and access control policies. You can improve server security by properly setting user, group, file and directory permissions, and controlling access using configuration files and firewall rules. In CentOS systems, you can use the code examples provided above to set permissions and access control policies.
The above is the detailed content of Permissions and access control strategies that you need to pay attention to before building a web server on CentOS. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Difference between centos and ubuntu
Apr 14, 2025 pm 09:09 PM
Difference between centos and ubuntu
Apr 14, 2025 pm 09:09 PM
The key differences between CentOS and Ubuntu are: origin (CentOS originates from Red Hat, for enterprises; Ubuntu originates from Debian, for individuals), package management (CentOS uses yum, focusing on stability; Ubuntu uses apt, for high update frequency), support cycle (CentOS provides 10 years of support, Ubuntu provides 5 years of LTS support), community support (CentOS focuses on stability, Ubuntu provides a wide range of tutorials and documents), uses (CentOS is biased towards servers, Ubuntu is suitable for servers and desktops), other differences include installation simplicity (CentOS is thin)
 Centos shutdown command line
Apr 14, 2025 pm 09:12 PM
Centos shutdown command line
Apr 14, 2025 pm 09:12 PM
The CentOS shutdown command is shutdown, and the syntax is shutdown [Options] Time [Information]. Options include: -h Stop the system immediately; -P Turn off the power after shutdown; -r restart; -t Waiting time. Times can be specified as immediate (now), minutes ( minutes), or a specific time (hh:mm). Added information can be displayed in system messages.
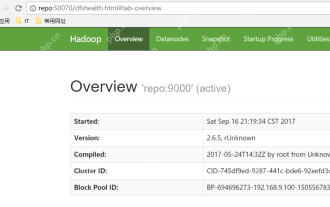 Hadoop pseudo-distributed cluster construction
May 07, 2025 pm 04:45 PM
Hadoop pseudo-distributed cluster construction
May 07, 2025 pm 04:45 PM
Software preparation I am using a virtual machine with CentOS-6.6, with the host name repo. Refer to the steps to install a Linux virtual machine in Windows, I installed JDK in that virtual machine, refer to the guide to installing JDK in Linux. In addition, the virtual machine is configured with a key-free login itself, and the settings for configuring key-free login between each virtual machine are referenced. The download address of Hadoop installation package is: https://mirrors.aliyun.com/apache/hadoop/common/. I am using hadoop 2.6.5 version. Upload the Hadoop installation package to the server and unzip [root@repo~]#tarzxv
 Centos configuration IP address
Apr 14, 2025 pm 09:06 PM
Centos configuration IP address
Apr 14, 2025 pm 09:06 PM
Steps to configure IP address in CentOS: View the current network configuration: ip addr Edit the network configuration file: sudo vi /etc/sysconfig/network-scripts/ifcfg-eth0 Change IP address: Edit IPADDR= Line changes the subnet mask and gateway (optional): Edit NETMASK= and GATEWAY= Lines Restart the network service: sudo systemctl restart network verification IP address: ip addr
 Centos stops maintenance 2024
Apr 14, 2025 pm 08:39 PM
Centos stops maintenance 2024
Apr 14, 2025 pm 08:39 PM
CentOS will be shut down in 2024 because its upstream distribution, RHEL 8, has been shut down. This shutdown will affect the CentOS 8 system, preventing it from continuing to receive updates. Users should plan for migration, and recommended options include CentOS Stream, AlmaLinux, and Rocky Linux to keep the system safe and stable.
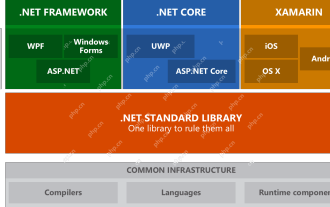 .NET Core Quick Start Tutorial 1. The beginning: Talking about .NET Core
May 07, 2025 pm 04:54 PM
.NET Core Quick Start Tutorial 1. The beginning: Talking about .NET Core
May 07, 2025 pm 04:54 PM
1. The Origin of .NETCore When talking about .NETCore, we must not mention its predecessor .NET. Java was in the limelight at that time, and Microsoft also favored Java. The Java virtual machine on the Windows platform was developed by Microsoft based on JVM standards. It is said to be the best performance Java virtual machine at that time. However, Microsoft has its own little abacus, trying to bundle Java with the Windows platform and add some Windows-specific features. Sun's dissatisfaction with this led to a breakdown of the relationship between the two parties, and Microsoft then launched .NET. .NET has borrowed many features of Java since its inception and gradually surpassed Java in language features and form development. Java in version 1.6
 IIS: An Introduction to the Microsoft Web Server
May 07, 2025 am 12:03 AM
IIS: An Introduction to the Microsoft Web Server
May 07, 2025 am 12:03 AM
IIS is a web server software developed by Microsoft to host websites and applications. 1. Installing IIS can be done through the "Add Roles and Features" wizard in Windows. 2. Creating a website can be achieved through PowerShell scripts. 3. Configure URL rewrites can be implemented through web.config file to improve security and SEO. 4. Debugging can be done by checking IIS logs, permission settings and performance monitoring. 5. Optimizing IIS performance can be achieved by enabling compression, configuring caching and load balancing.
 Postman Integrated Application on CentOS
May 19, 2025 pm 08:00 PM
Postman Integrated Application on CentOS
May 19, 2025 pm 08:00 PM
Integrating Postman applications on CentOS can be achieved through a variety of methods. The following are the detailed steps and suggestions: Install Postman by downloading the installation package to download Postman's Linux version installation package: Visit Postman's official website and select the version suitable for Linux to download. Unzip the installation package: Use the following command to unzip the installation package to the specified directory, for example /opt: sudotar-xzfpostman-linux-x64-xx.xx.xx.tar.gz-C/opt Please note that "postman-linux-x64-xx.xx.xx.tar.gz" is replaced by the file name you actually downloaded. Create symbols





